Why?
Have you ever run a command on one of your hosts and then wanted to retrieve it later? Then couldn’t remember where you ran it, or it’s lost from your history?
This happens to me all the time. The other day I was hunting for a command I was convinced I’d run, but wasn’t sure where it was or whether it was stored.
So I finally wrote a service that records my every command centrally.
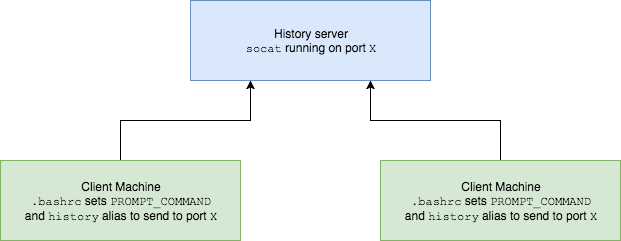
Here’s an overview of its (simple) architecture.
What?
This stores your bash history on a server in a file.
The service runs on a port of your choosing, and if you have some lines in your ~.bashrc file then it will all work seamlessly for you.
There’s some basic authentication (shared key) to prevent abuse of the service.
How?
To set up, see the README.
Requirements
Needs socat installed, and bash version 4+.
Related posts
Ten Things About Bash
Ten More Things About Bash
PS
I need help to improve this – see the README.
PPS
If you ask nicely I might host it for you, without warranty etc..
If you want to learn more about bash, read my book Learn Bash the Hard Way, available at $5:

This is horribly insecure and command history can contain some seriously valuable information, passwords, connection strings, etc. Why not do this with git/github? Put .bash_history in a repo, set PROMPT_COMMAND to commit, push, and pull the repo. This has numerous advantages: no dependency (everybody has git), free hosting available from multiple providers (public and private repos), no poking holes in firewalls for ports, no managing secrets, no service running and listening, bunch more reasons including those listed in your bugs/todo.
You are assuming this is used primarily over the internet… I did something similar a few years back to manage a lot of servers enclosed in their own network. Since the risk of damage is a lot smaller (can only be abbused by people having administrative access to servers or physical access to the server-room, I dont see the point in enlarging the security risk by using a service like github.
PS: this comment is only to show that it might be better to perform constructive feedback instead of dismissing the whole idea because you don’t have enough knowledge of the field in which it is used.
nice!
I’ve added it to all nodes I’m handling, to all users. now let’s the spying game begin…
also – I’ve modified a little: added the host and user name and a timestamp
I’ll update (hopefully, if I remember) in a few days to see if indeed it worked, or did it collapse my server machine…